There is increasing chatter among the world’s major military powers about how space is fast becoming the next battleground. China, Russia, and the United States are all taking steps that will ultimately result in the weaponisation of space. Any satellite that can change orbit can be considered a space weapon, but since many of the possible space-based scenarios have yet to occur, cybersecurity experts, military commanders, and policymakers do not fully understand the range of potential consequences that could result.
During the Cold War, the Soviet Union was interested in paralysing America’s strategic forces, strategic command, and control and communications, so that its military command could not communicate with its forces. They would do so by first causing electromagnetic pulse (EMP) to sever communication and operational capabilities, and then launch a mass attack across the North Pole to blow up US Intercontinental Ballistic Missiles (ICBMs).
In 1967, the US, UK and Soviet Union signed the Outer Space Treaty, which was either ratified by or acceded to 105 countries (including China). It set in place laws regarding the use of outer space and banned any nation from stationing nuclear warheads, chemical or biological weapons in space. However, the Treaty does not prohibit the placement of conventional weapons in orbit, so such weapons as kinetic bombardment (i.e. attacking Earth with a projectile) are not strictly prohibited.
North Korea’s Kim Jong-Un took a page from the old Soviet playbook by launching two satellites (in 2012 and 2016) that can threaten the US by (in theory, at least), guiding its ICBMs to attack the US with an EMP as part of a larger surprise assault aimed at crippling the US military. The two North Korean satellites that orbit over the US are on trajectories consistent with surprise EMP attack. The purpose of the satellites is to position North Korea to be able to play a cyber-era version of battleship diplomacy—with one of the two satellites always being close to being in orbit directly over the US at any point in time.
An EMP attack could severely disrupt America’s electricity grid, telecommunications, transportation network, and other forms of critical infrastructure. This is the unspoken part of Kim’s strategy, and America’s concern about North Korea. A single warhead could black out the US national electric grid and other life-sustaining critical infrastructure for more than a year, threatening mass starvation and potential societal collapse.
China sees space warfare as its best chance to directly compete with the US militarily, since it has no blue water navy, nor anywhere near the assets and firepower capability that the US military has. Rather than trying to match the US Navy and Air Force, China believes it can gain an advantage through production of specialised missiles, spacecraft, and platforms to send to the moon. Many Chinese military analysts see space warfare as inevitable, and argue that since it will become the centre of gravity in future wars, it must be seized and controlled so as to achieve space supremacy.
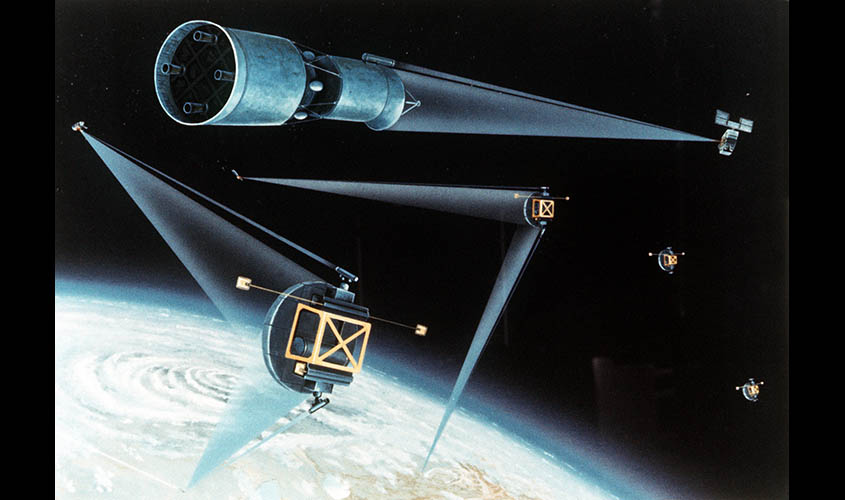
In 2015, the People’s Liberation Army published the book Light War, which assigned a central role to fighting future wars using lasers. The book argues that future warfare will be dominated by combining Big Data analytics using cyber warriors armed with artificial intelligence, robot lasers, and directed energy weapons. The Chinese effort could neutralise decades of investment by the US in its own directed-energy weapons, which are expected to be deployed in the early 2020s (high-powered compact laser guns are slated for deployment in the 2030s). China’s disclosures about the coming “weaponisation of space” should greatly concern US and allied defence planners. The US may soon have no choice but to change its long-held policy of not deploying arms in space.
As evidence that the Chinese government is peering far into the future, it plans to create an entire system of quantum-enabled, satellite-based communication that relies on entanglement (grouping particles together). The Chinese government seeks to build an entirely new kind of Internet that is completely secure and impervious to hackers. This year, Chinese scientists set a new distance record for beaming a pair of entangled particles—photons of light that behave like twins and experience the exact same things simultaneously, even though they are separated by great distances. The principle is called quantum entanglement, which is one of the subatomic world’s strangest phenomena. By launching a group of quantum-enabled satellites, China hopes to create a super-secure network that uses an encryption technique based on the principles of a field known as quantum communication.
Space warfare (or the prospect of it) has propelled hacking to a whole new dimension. Among the US National Aeronautics and Space Administration’s cyber concerns are hackers wanting to breach communications between its ground-based operations and one of its 65 spacecraft transmitting research data. Its nightmare is a direct cyberattack on its satellites. In 2016, NASA reported 1,484 “cyber incidents”, including hundreds of attacks executed from websites or web-based applications, as well as the loss or theft of computing devices. Its cybersecurity teams are working to “harden” old Industrial Control Systems, such as those used to launch spacecraft.
The next war between major powers is likely to be fought in space, or, at a minimum, have a space-based component. As is the case with cybersecurity policy on Earth, cybersecurity in space clearly needs to be brought into the 21st century. The current state of affairs is riddled with gaps, inconsistencies, and vulnerabilities. By undertaking to develop an international multi-stakeholder cybersecurity regime, the space industry could play an increasingly influential role in developing international standards and establishing a strong sustainable knowledge base in the cybersecurity domain. However, given the demise of the Outer Space Treaty, that may just be wishful thinking.
Daniel Wagner is CEO of Country Risk Solutions and author of Virtual Terror.