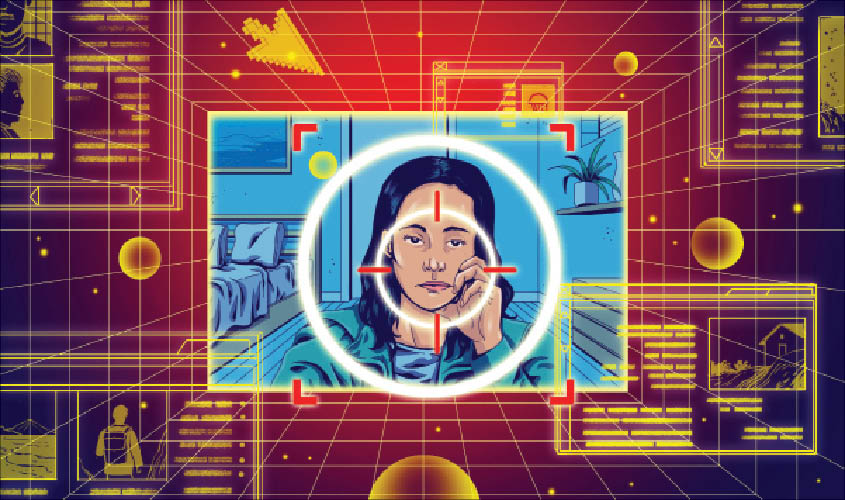
If there’s one lesson to learn about digital privacy, it’s that we can never grow complacent. Even if we secure our data so we are not tracked online, the ad tech industry will find ways to monitor our digital activities.
And so it is with the rise of so-called fingerprinting, which security researchers are calling a next-generation tracking technology.
What is it exactly? Fingerprinting involves looking at the many characteristics of your mobile device or computer, like the screen resolution, operating system and model, and triangulating this information to pinpoint and follow you as you browse the web and use apps. Once enough device characteristics are known, the theory goes, the data can be assembled into a profile that helps identify you the way a fingerprint would.
“Get enough of those attributes together and it creates essentially a bar code,” said Peter Dolanjski, a product lead for Mozilla’s Firefox web browser, who is studying fingerprinting. “That bar code is absolutely uniquely identifiable.”
And here’s the bad news: The technique happens invisibly in the background in apps and websites. That makes it tougher to detect and combat than its predecessor, the web cookie, which was a tracker stored on our devices. The solutions to blocking fingerprinting are also limited.
Security researchers discovered fingerprinting as a tracking method about seven years ago, but it was rarely discussed until recently. Only about 3.5% of the most popular websites use it today for tracking, but that’s up from about 1.6% in 2016, according to Mozilla. And an unknown number of mobile apps also use fingerprinting.
All of this is not a reason to panic, but it is a reason to be concerned. As fingerprinting becomes more popular, here’s what you need to know about it and what we can do.
How did we get here?
Over the last few years, tech companies like Apple and Mozilla introduced aggressive privacy protections inside their web browsers. Tracker blocking is built into the Safari and Firefox browsers to make it harder for advertisers to follow us around the web and serve targeted ads. That thwarted traditional tracking methods like cookies and pixels that were embedded inside social media buttons.
Because many of those technologies became blocked by default, advertisers had to find a different way to track people.
How does fingerprinting work?
Let’s get technical for a moment. Fingerprinting takes advantage of a fundamental way that apps and websites talk to our devices.
When you browse the web, your browser automatically gives websites some information about your hardware. That’s partly because a website needs to know things like the resolution of your screen so it can load a page in the correct window size.
Similarly, when you install a mobile app, the operating system shares some information about your hardware with the app. That’s partly because an app needs to know what type of phone you use so it can adapt to the processor speed and screen size.
There are restrictions to the data that apps and websites can get about your device. On iPhones and Android phones, for example, you must give an app permission to gain access to your location data, your camera and microphone. Similarly, many browsers also require your permission before a website can have access to those sensors.
But fingerprinting collects seemingly innocuous characteristics that are generally shared by default to make apps and websites work properly.
With enough information gathered, fingerprinting can be very reliable. In a study last year in France, researchers found that about one-third of digital fingerprints they collected were unique and therefore identifiable. In a 2017 study, researchers at Lehigh University and Washington University tested a fingerprinting method that identified 99% of users.
Privacy advocates say fingerprinting is abusive because in contrast to cookies, which people can see and delete, you generally cannot tell it is happening and cannot opt out of it.
“It’s really a black box,” said Casey Oppenheim, chief executive of Disconnect, a company that develops tracker blocking tools.
What can I do?
The solutions for preventing fingerprinting are relatively new and some are still in development. It is hard to tell how effective they are since fingerprinting happens invisibly. But taking advantage of the solutions will give you peace of mind if you care about privacy.
Here are some solutions for blocking browser fingerprinting.
—Apple users have protections in Safari for computers and mobile devices.
For those who use iPhones and Macs, Apple introduced a fingerprinting defense mechanism in its Safari browser last year. It basically makes many Macs and iPhones look the same to a website by sharing the bare minimum of information that the site needs to load properly. (For example, if you are using MacOS 10.14.5, the browser will tell the website only that you are using MacOS 10.14.)
To take advantage of this defense, just make sure you are running a recent version of the iPhone and Mac operating systems.
—Android users and Windows users can try the Firefox web browser.
Mozilla introduced fingerprint blocking in its Firefox browser this year, but the feature can prevent content for some websites from loading or a shopping site from processing a payment properly, so it’s not turned on by default, the company said.
Mozilla said it was making progress and expected to block fingerprinting by default in a future release. For now, you can enable the feature by opening the browser preferences, clicking on the privacy and security page, selecting “Custom” and checkmarking “fingerprinters.”
Google announced this year that it planned to introduce fingerprint defense for its Chrome browser, but it did not specify when the feature would be released.
—Other desktop browsers can install an add-on.
Disconnect offers a tracker blocker for web browsers that includes fingerprint defense. It’s a downloadable add-on that works with Google’s Chrome browser, among others. I’ve used it on my desktop browsers for years, and it works well. But it also has its flaws: Occasionally, the tool breaks shopping sites, and I have to disable Disconnect to do things like add items to my shopping cart.
Mobile fingerprinting is a different beast.
Fingerprinting can be done directly inside apps, without people easily seeing what data an app is gathering in the background or when it runs. One example of this surfaced in 2017 when The New York Times revealed that Uber used a form of fingerprinting inside its iPhone app to identify users even after they erased content from their devices.
Fingerprint defenses in mobile apps are only beginning to emerge. Here’s one example:
—Disconnect offers mobile apps for blocking trackers inside other apps.
For iPhones and Android devices, Privacy Pro and Disconnect Premium can analyze app activities on your device to detect and block trackers, including fingerprinters. Once the Disconnect apps are installed and activated, the tracker blocking happens automatically.
The problem with the Disconnect apps is that it is difficult to decipher which specific apps are doing the fingerprinting so that you can delete them. When I recently opened my Privacy Pro app, it was unable to say which app was doing what because of restrictions in the iPhone’s software architecture. Disconnect said it was working on making the app easier to use.
So what’s the most practical thing you can do for mobile? Start by deleting apps you rarely use, especially the ones from obscure brands. Free apps are most likely to be loaded with trackers, though some paid ones track you, too.
Fingerprinting is a complex topic since the tracking method applies to both the web and mobile apps. But don’t stress if you don’t protect yourself right away: Just learning about it now means you are ahead of the curve.
© 2019 The New York Times